Cyber Insurance – What does cyber insurance covers?
July 3, 2019
Ian Westwood
July 3, 2019
Ian Westwood
As Robert Mueller (FBI Director 2012) put it: “There are only two types of companies: those that have been hacked and those that will be”
Virtually every business relies on data and computer systems. When these systems experience a virus or other computer attack (cyber attack), a business is at real risk of losing critical information that is essential to daily operations and potentially exposing itself to third-party liability. Since data can be sold at extremely high prices in the black market, hackers have strong motivation to hunt after these data.
Statistics show that for companies that they were hacked in the past, there is a 65% possibility for them to be re-hacked in the future.
In 2018 the Cyprus Government will have to fully comply with the Personal Data Protection Policies and the newly established institution of the Commissioner for Personal Data Protection will be fully activated. This practically means that during information leakage, all companies are obliged to inform not just the Authorities of Data Protection but also all of their clients, employees, suppliers, etc. who were directly or indirectly involved in the leakage.
The Cyber Insurance helps clients prevent and safeguard against sensitive data breaches, computer hacking, employee error and more.
Even if your company applies the most stringent security policies and uses the most advanced firewall software, the danger still lurks. Cybercrime is the most rapidly evolving crime industry in the world.
The usual methods hackers are using to steal data are:
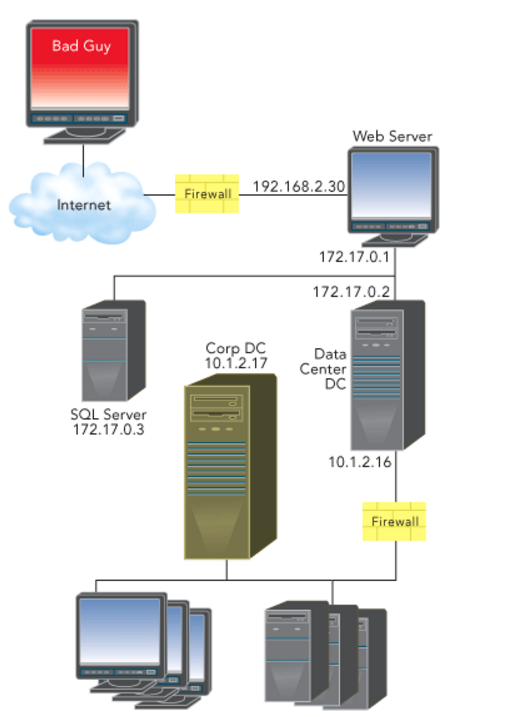
Tools hackers use to achieve their aims:
Some of these malicious programs cannot be detected because of they:
All companies possessing data like names, addresses, bank accounts, credit cards or personal information of clients face a significant risk of being hacked.
Small businesses are even more likely to be hacked since they have limited security and technical resources. Light security makes them easy targets.
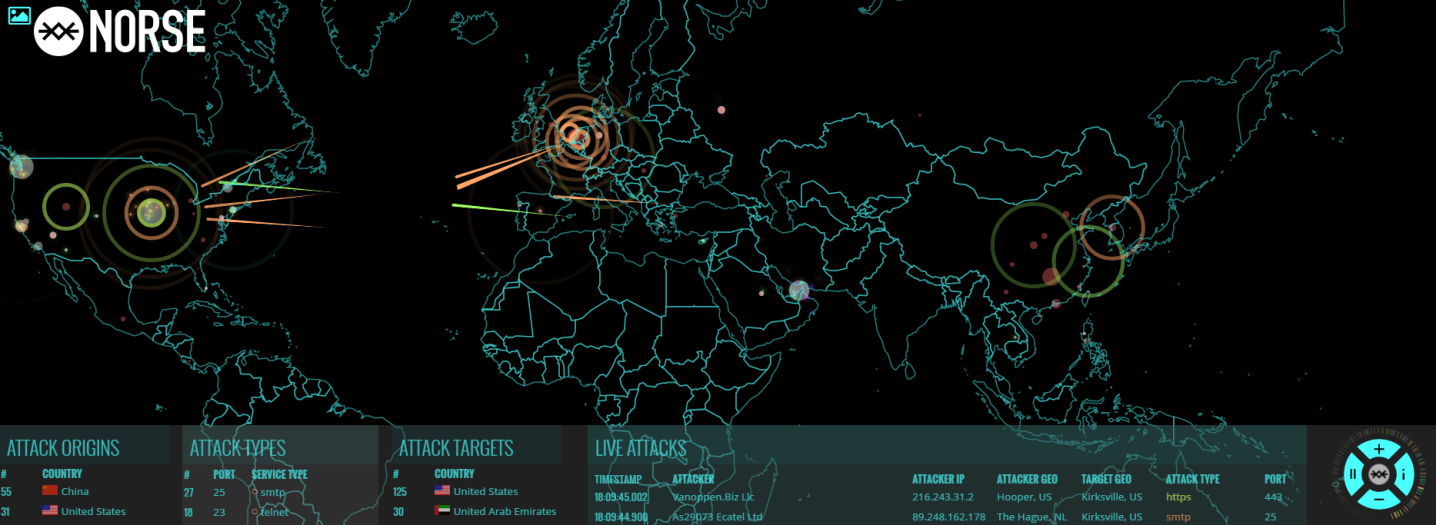
As the Norse Attack Map (map.norsecorp.com) shows, companies from all over the world are attacked on a daily basis.
In 2014 one of the most prestigious corporate service providers in Cyprus become a victim of a Cyber-Attack orchestrated by one of the most notorious hackers in the world. The hacker phoned the director of the company demanding a ransom of €10.000.000 in bitcoins. He said that he possessed Sensitive Data of the company’s clients and that in case his demands were not met, he would release them resulting in incalculable damages for both company and clients. The director was not convinced, but 10 minutes later he received stolen personal data on his computer. Immediately the director communicated with our partners in order to handle the crisis. A crisis management was called in order to deal with the crisis, while NYA experts come from London in order to proceed with ransom negotiations. The IT consultants were able to detect that the hacker had inserted a USB in a computer connected with the network of the company 2 years ago, thus extracting data of two Gigabytes. The NYA managed to reduce the ransom fee from Ƀ € 10,000,000 to Ƀ € 900,000 but the company finally agreed to pay Ƀ € 1,100,000. The payment will be made in a period of 6 years.
The direct damage of the company is:
Economic loss due to the halting of the company’s operations.
Crucial software programs were unavailable for days (e.g. financial company in Nicosia, loss of 35,000 euro due to the pausing of operations).
The server had to stop working until the problem was detected and solved.
Significant economic damage for the restoration of data.
Loss of data e.g. personal data, sensitive data that might help competitors (e.g. pricing policy, operating expenses, the contact information of clients, etc)
Damage on data
Allowing attackers to view and alter the project database and information from the WinCC server.
Third party lawsuits for leakage of sensitive information of clients.
Log keystrokes to steal user credentials to bank login pages
Leaks of confidential information (e.g. 30% of the lawsuits against clinics in the USA were due to leakage of information).
Related lawsuits against the directors of the company are also covered.
Online Defamation & Copyright trademark infringement.
Hackers might find information on illegal acts (e.g. money laundering) and start threatening that the information will be disclosed to public authorities.
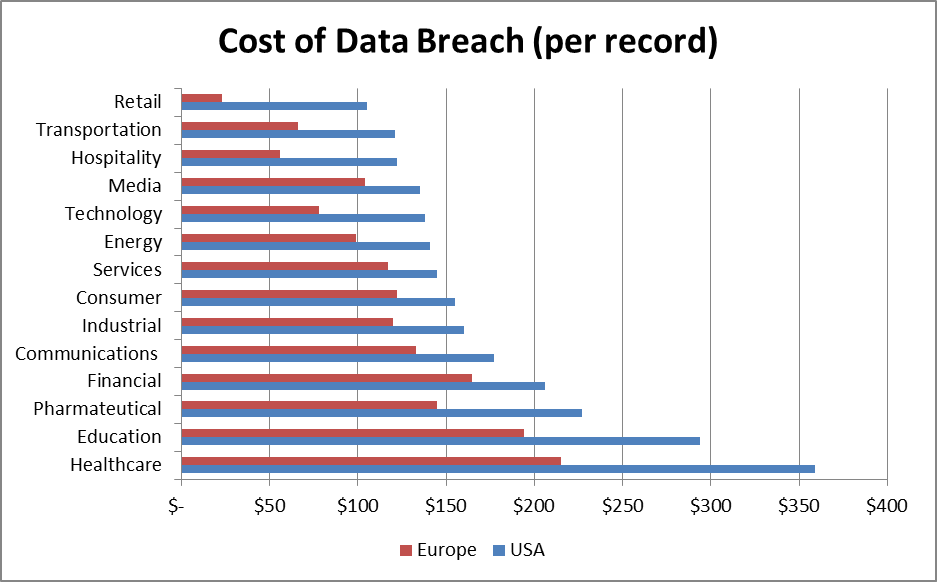
There have been many efforts to determine the real cost incurred from loss of records. In 2014 the Ponemon Institute prepared a report presenting the cost of loss for each record in the USA and Europe, with results given below (Source 2014 – Cost of Data Breach Study Global – Ponemon Institute Research Report).
The policies of Pitsas Insurances provide broad affordable cyber liability protection, specifically designed for the needs of your business to address the ever-growing thread of information security exposures.
The coverage includes the following categories of expenses:
In case an employee causes a problem to the software or to the database deliberately, then the insurance policy covers everything.
Conflicting cases:
The Cyber Edge insurance is usually combined with Crime Insurance (our package is called CrimeGuard Choice).
8.1.1. Coverage Highlights
To get a calculation of the cost of insurance, follow the link Cyber Insurance.
Pitsas Insurances,
03/07/2019